10 KiB
| title | subtitle | summary | tags | categories | published | featured | draft | |||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Malware Neutralization |
|
2023-11-07 | false | false |
Malware Neutralization
In this blog post, I introduce a novel concept known as Malware Neutralization. While the following discussion remains theoretical without practical implementation or a Proof of Concept (PoC), I guarantee its sensical and logical for a long-unsolved problem. The concept described uses a series of novel technologies that were not available in the past. However, recent advancements in the past years have made this concept at least theoretically feasible, which is the reason behind this blog post.
Motivation
In the early 21st century, a category of malware known as Injected File gained significant attention as one of the first types of cyberattacks to capture widespread interest. Unlike the sophisticated tactics employed in modern cyberattacks, Injected File attacks involve the modification of a file with malicious code, enabling it to be later executed and propagate itself. Over time, these attacks fell into relative obscurity, overshadowed by various factors.
One of the primary reasons for their decline is the effectiveness of antivirus and Endpoint Detection and Response (EDR) systems, which promptly remove any file detected with malicious components. Additionally, the prevailing trend among malicious actors shifted towards the creation of weaponized malware for mass distribution. Injected File attacks, which involve altering existing files, became less common. However, recent developments have indicated a resurgence of Injected File malware, as reported by Mandiant in 2021.
While the conventional response to such attacks has been the removal of all infected files, this may not always be the ideal solution. In some cases, these files hold significant importance for the system or the user. Recovering infected files has posed a persistent challenge over the years, with the most effective approach often involving the use of periodic backups. However, situations arise where backups are unavailable, or the original unmodified file is no longer accessible.
In the context of the recent advancements in technology over the past few decades, notably in the fields of Machine Learning, Deep Learning, and Program Synthesis, it has become evident that this long-standing problem may find a more effective solution through the proposed concept of Malware Neutralization.
Concept
Malware Neutralization represents an innovative paradigm - the removal of malicious components within binary files, encompassing software executables and documents, while preserving the integrity of legitimate components. This novel approach ensures that the "good" elements are retained, thereby allowing the file to maintain its intended functionality.
The process can be segmented into the following steps:
- Detection of Malicious Components
- Removal of Malicious Components
- Binary Restoration
Subsequent sections will delve into each of these steps, dissecting their technical intricacies.
Detection of Malicious Components
Detection of malicious components within binary files entails a formidable challenge. It demands a profound understanding of various malware infection techniques. Conventional methods like YARA signatures or heuristic-based detection, designed for rapid software classification, fall short in this context. A more rigorous approach is essential, one that ensures the identification of all malicious components. To this end, Machine Learning or Deep Learning models offer a promising path, as they can provide the agility and accuracy required for this complex endeavor.
Removal of Malicious Components
Once all malicious components have been successfully identified, the subsequent step involves their surgical removal from the binary. This may involve overwriting their locations with null bytes, particularly for executable binaries. Document files, such as OLEs or zip streams, might necessitate encoding/decoding for the removal process. One of the most challenging aspects of this step pertains to determining the extent of removal. In the absence of comprehensive evidence, we may need to contend with the possibility that malicious components span a significant portion of the binary, while our detection methods may only unveil a fraction of them. These dilemmas underscore the need for further research, particularly in defining the scope of removal, whether it entails the entire function or only a portion of what has been detected.
Binary Restoration
The final step, binary restoration, brings into play the concept of Program Synthesis. Some malware infection techniques exhibit strong ties to legitimate components, necessitating the recovery of removed components without disrupting the overall execution flow. Automatic Program Repair, a facet of Program Synthesis, offers a potential solution. This involves generating assembly-level patches to rectify identified issues, ideally without impeding the functionality of other legitimate components.
This step introduces its own set of challenges, such as establishing constraints for reinstating the removed segments. In the context of assembly, this could involve maintaining stacks and registers, although this remains open to debate. Another challenge concerns the algorithmic approach for determining the correct "fixes". This could involve logical analysis of program semantics, Machine Learning, Deep Learning, or other methodologies, with a focus on effectiveness, robustness, and speed. While Program Synthesis is the proposed technology for this step, alternative approaches might emerge to effectively restore and repair the removed components.
History
In this section, we'll rewind to the early years of the 21st century and delve into the prevalent trend of Injected File Viruses.
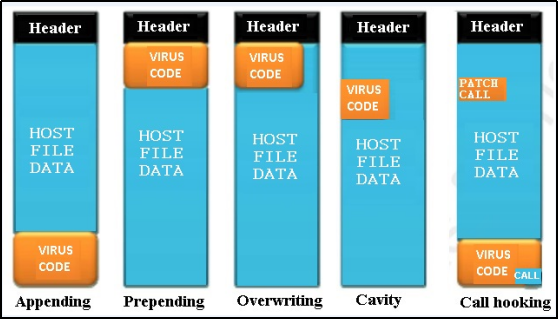
The most common method employed by Injected File Viruses is the modification of the entry point within a file. This alteration redirects the entry point to the malware code, ensuring that when the file is executed, the malicious components take precedence. Variants of this method may involve placing the malware at different locations within the file or utilizing an inline hook to control the flow of the program and direct it to the malware components. To help visualize the underlying logic of these malware types, consider the diagram below:
Although some research has documented these behaviors, it's important to note that these infection techniques, while seemingly straightforward, are not only easy to detect but also to rebuild or reconstruct the file. This process often requires a profound understanding of malware and manual binary patching. It's worth mentioning that the point at which antivirus software began to accept the removal of infected files remains unclear. However, it was a logical step towards enhancing system protection.
As technology advanced, the prevalence of Injected File Viruses began to wane, gradually losing their prominence to more insidious forms of malware. Modern threats, such as stealthy stealers, cryptojacking, and the destructive power of ransomware, took center stage, leveraging sophisticated techniques to evade detection and wreak havoc on systems.
However, even in this evolving landscape, the concept of Infected File Viruses remains relevant, albeit with a different classification. Concrete evidence has emerged, highlighting that documents in various formats (e.g., Word, Excel, PDF) can serve as vessels for malicious components. These files, seemingly innocuous, can harbor hidden threats.
Additionally, Trojans represent another manifestation of Infected Files. Trojans often pose as legitimate programs, concealing their malevolent components. They exemplify the enduring nature of Infected File malware, adapting to new forms and evading detection while posing significant threats to cybersecurity.
Conclusion
In summary, Malware Neutralization emerges as a progressive process designed to neutralize binary files, encompassing software executables and documents, by selectively removing malicious components while preserving the overall functionality of the file. This innovative approach paves the way for a fresh avenue of research in the realm of malware mitigation. While its potential is intriguing, its efficiency remains to be substantiated. The decision to delve deeper into this topic in the future will be contingent on the urgency of finding a solution, its demonstrated efficacy, and its capacity to address the evolving landscape of malware threats. Undoubtedly, the ability to neutralize (recover) infected files represents a long-awaited solution that could reshape the landscape of cybersecurity. As the field progresses, the quest for robust and effective methods to combat malware continues, with Malware Neutralization offering a promising direction for further exploration.
Research and Future Prospects
This blog post extends an open invitation to researchers interested in exploring the concept of Malware Neutralization. The guidelines provided herein, covering various domains such as Malware Analysis, Program Analysis, Binary Analysis, Assembly, Machine Learning, Deep Learning, Large Language Modeling, Program Synthesis, Program Semantics offer a comprehensive roadmap for tackling this multifaceted challenge. Researchers are encouraged to begin by addressing each aspect individually and subsequently integrating solutions. A pivotal milestone in this journey involves the development of a Proof of Concept (PoC) to validate the practicality of the concept.
I may or may not undertake further research in this field, but welcome and anticipate engagement from researchers keen on taking this concept to the next level, thereby contributing to the ongoing evolution of software security.